Fine-grained access control in API Gateway with Cognito groups & Lambda authorizer
|
In security and access control, authentication and authorization mean two distinct but related things. Authentication verifies the identity of a user or system. Authorization determines what actions an authenticated user is allowed to perform in your system. API Gateway has built-in integration with Cognito, but it doesn’t provide any fine-grained authorization out-of-the-box. By default, a Cognito authorizer only checks if a user’s bearer token is valid and that the user belongs to the right Cognito User Pool. Here are many ways you can implement a fine-grained authorization with API Gateway. Here are three that I have come across over the years:
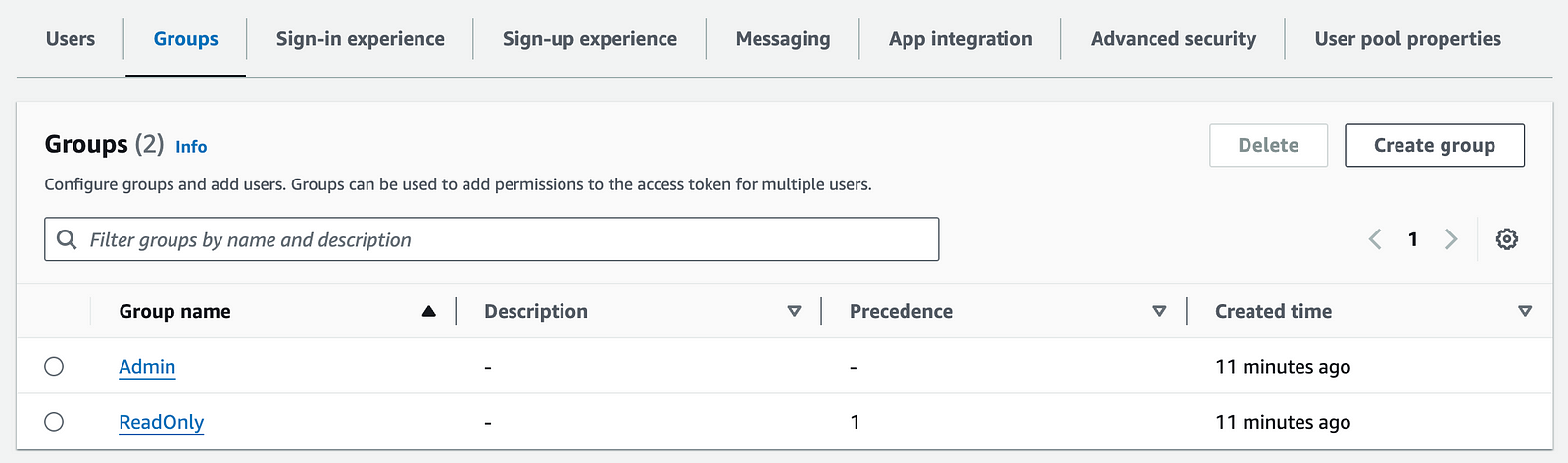
Over the next few weeks, let’s look at these approaches in-depth and then compare them at the end. Today, let’s look at Lambda authorizer with Cognito groups. Model roles with Cognito groupsIn Cognito, you can use groups to model the different roles in your system, e.g.
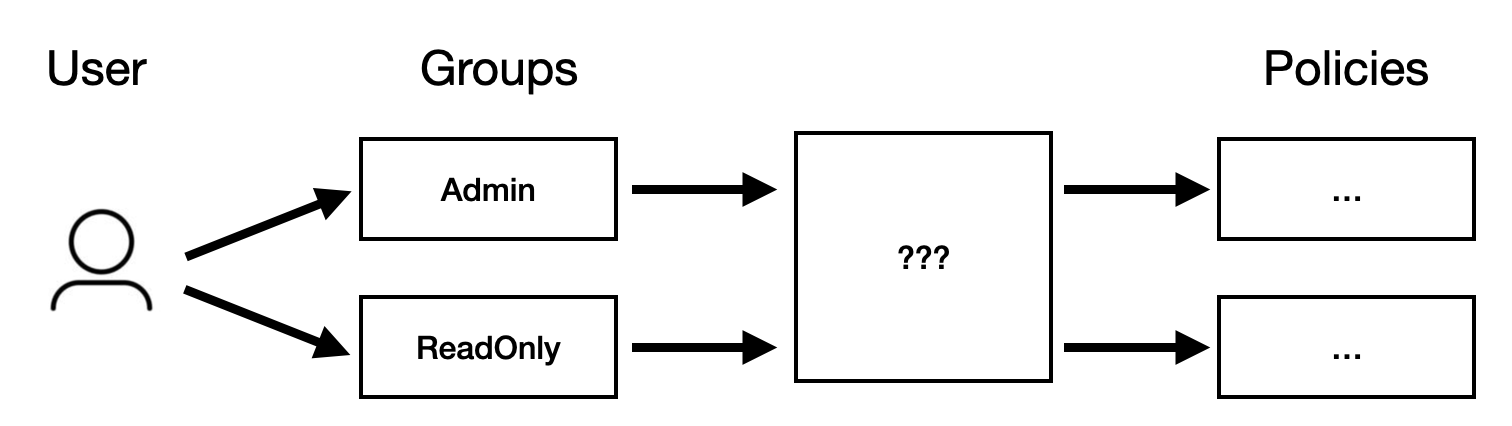
Users can belong to more than one group at once, just as they can have multiple roles within a system. Cognito encodes the groups a user belongs to in the ID token. If you decode the ID token, you will see something like this: Here, we can see the user belongs to both the Lambda authorizerA Lambda authorizer can use this information to generate its policy document. As a reminder, a Lambda authorizer can return a policy document like this: So, we need to take the list of groups a user belongs to and turn them into a set of policy statements.
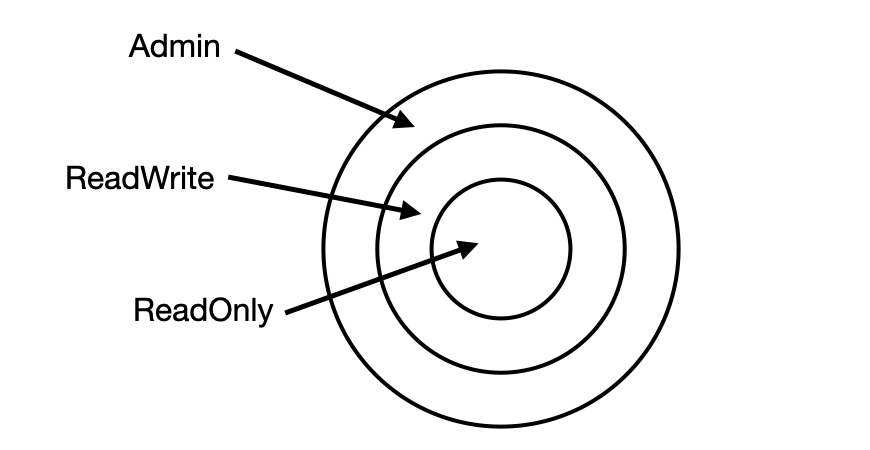
One approach is to keep a mapping in your code like this. In many systems, there are a small number of roles that supersede each other. That is, they are hierarchical, and a higher role has all the permissions of a lower role plus some.
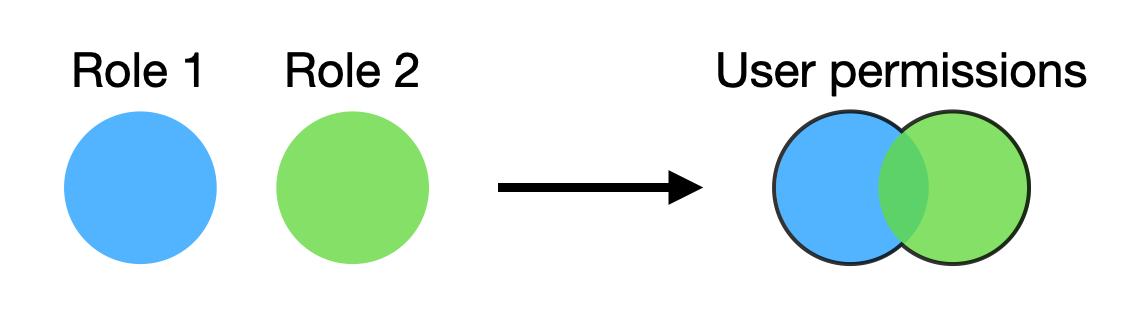
In this case, we need to find the most permissive role that the user has. But what if the roles are more lateral? That is, a user’s permissions are derived from all its roles.
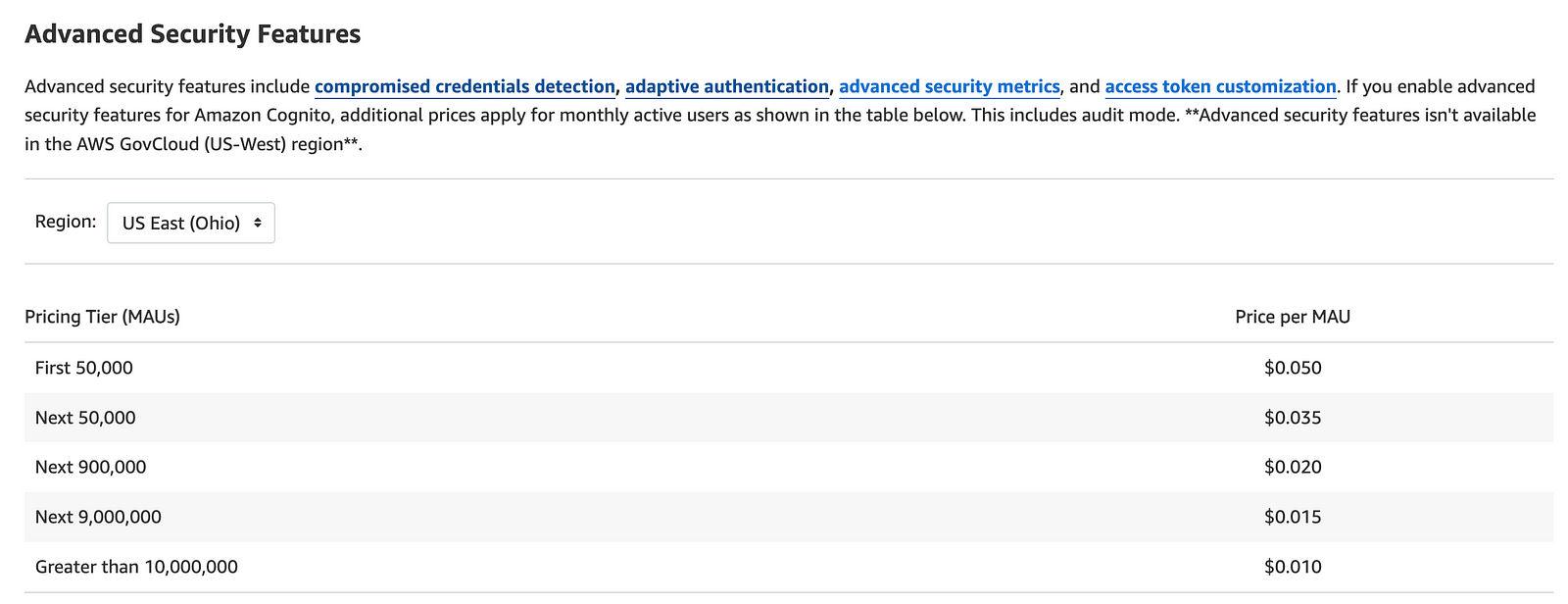
Well, that’s easy enough to accommodate. ConclusionThis is my preferred approach for simple use cases. It’s easy to follow and test and makes no API calls (i.e. no extra latency overhead). Furthermore, it does not require Cognito’s Advanced Security Features, which are charged at a much higher rate [2]. This makes it a very cost-efficient approach.
However, using a Lambda authorizer means you need to think about cold starts and their impact on user experience. Also, the roles and policies are static. Whilst it’s good enough for most simple use cases, it cannot (easily) support more advanced use cases. For example, if you need to allow users to create custom roles while maintaining the tenant boundary. Amazon Verified Permissions is a better fit for more advanced use cases. More on it later. Links |
Master Serverless
Join 17K readers and level up you AWS game with just 5 mins a week.
AI agents can now scan an entire open-source codebase for exploitable vulnerabilities in hours. Frontier models carry the complete library of known bug classes in their weights. So you can simply point an AI agent at a codebase and tell it to find zero-days. This isn't theoretical. Willy Tarreau, the HAProxy lead developer, reports that security bug reports have jumped from 2–3 per week to 5–10 per day. Greg Kroah-Hartman, the Linux kernel maintainer, described what happened: "Months ago, we...
Lambda Durable Functions makes it easy to implement business workflows using plain Lambda functions. Besides the intended use cases, they also let us implement ETL jobs without needing recursions or Step Functions. Many long-running ETL jobs have a time-consuming, sequential steps that cannot be easily parallelised. For example: Fetching data from shared databases/APIs with throughput limits. When data needs to be processed sequentially. Historically, Lambda was not a good fit for these...
Step Functions is often used to poll long-running processes, e.g. when starting a new data migration task with Amazon Database Migration. There's usually a Wait -> Poll -> Choice loop that runs until the task is complete (or failed), like the one below. Polling is inefficient and can add unnecessary cost as standard workflows are charged based on the number of state transitions. There is an event-driven alternative to this approach. Here's the high level approach: To start the data migration,...